
ISO 27001
Specifies requirements for an ISMS to manage sensitive info securely
Deskpro Trust Center
Deskpro is committed to safeguarding your data and your customers with comprehensive and transparent security programs and frameworks.

Specifies requirements for an ISMS to manage sensitive info securely

Reports on control effectiveness over time for Trust Services Criteria

Protects payment card holder data from breaches & theft

EU regulation protecting citizens' data & privacy rights

US law securing protected healthcare information

UK government initiative promoting cloud use in public sector with a procurement framework

Promotes secure cloud environments via best practices

Scheme ensuring basic level of cybersecurity measures in place

Enhancing CA residents' privacy rights through stronger consumer protections.
Deskpro is committed to constantly maintaining knowledge of the evolving application security landscape and ensuring that security best practices are upheld across the whole organization.
We provide customers with a vast array of customizations including customers being able to choose how to deploy Deskpro, either on Cloud or On-Premise (self-hosted), and where your data is stored.
For our cloud hosting, we use industry-leading AWS.

The aim of Deskpro's security practice is to prevent any unauthorized access to customer data.
We are always looking at ways in which we can improve the security of Deskpro taking exhaustive steps to find and mitigate risks.
Regular management security reviews are in place to address any areas that we believe can be improved upon and further secured. Implementation of this may be through new security certification, compliance or 3rd party testing to ensure best practices and improve security across the whole of Deskpro.

Learn more about how Deskpro ensures the data in your help desk is always secure, whether you choose Cloud or On-Premise deployment.

GDPR is the most significant change to European data privacy legislation in over 20 years. Deskpro provides tools in the product, as well as our DPA, allowing you to be GDPR compliant using Deskpro.

Deskpro maintains a high level of availability on the cloud platform, averaging over 99.9%. You can check the status of the cloud software on our publicly available status page.
Our cloud service data-center provider (AWS) operates state-of-the-art, ISO27001, PCI DSS Level 1, HIPAA, EU-US Privacy Shield & SOC 2 Type compliant data centers. Automated fire detection and suppression systems are installed in networking, mechanical, and infrastructure areas. All AWS data centers are constructed to N+1 redundancy standards.
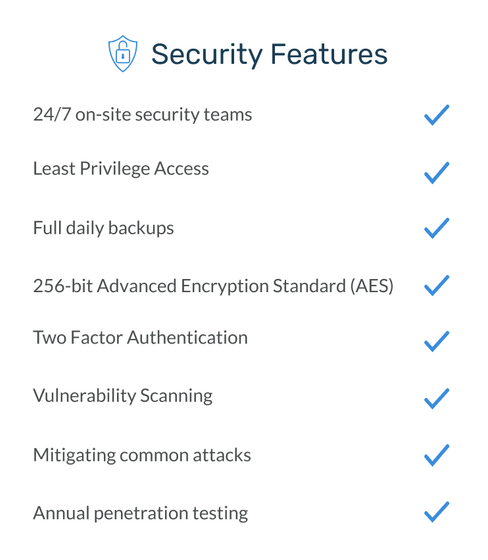
Our data center facilities have 24/7 on-site staff, physical access points to server rooms covered by CCTV, biometric security procedures, and round-the-clock surveillance monitoring to maintain protection against unauthorized entry and physical security breaches. They also require background checks for all employees as part of the pre-employment screening process.
AWS's Global Security Operation Centers conducts 24/7 monitoring of data center access activities, with electronic intrusion detection systems installed in the data layer. Systems constantly monitored by Deskpro Security Team.
Deskpro offers deployment of Cloud accounts onto data centers located in either the US, EU or UK. Customers can choose which region they wish to exclusively host their data in, as standard. *Enterprise plan customers can choose to host in 1 of 22 countries around the world.
Each facility is equipped with an uninterruptible power supply (UPS) and backup generators, in case of power disruption.
Each of our Data centers have a controlled Perimeter Layer with 24/7 on-site security teams, restricted and controlled physical access, multi-factor authentication, electronic intrusion detection systems and door alarming.
Deskpro's Security Team are distributed across the globe. They provide 24/7 monitoring and response to security incidents and alerts.
Deskpro’s public-facing network is protected by Cloudflare Enterprise which acts to filter all incoming traffic from the internet. Public-facing email servers are protected by AWS Shield, which similarly monitors and filters incoming traffic from the internet. No other services or access is provided to the public internet.
Within Deskpro’s internal private network, that is not accessible from the public internet, we employ AWS security groups and IAM controls to lock down communication between components so access to services must be granted explicitly on an as-needed basis. We make it impossible for systems to interact with each other without our explicitly configuring it and planning for it.
Deskpro system audit logs are always maintained and checked for anomalies and we use contracted third-party DDoS providers to protect from distributed attacks. Including both AWS Shield Guards and Cloudflare.
Access to hosting servers and live environments are provided on least privilege access. A very limited number of employees have access to live environments, which also require multiple levels of security access.
Deskpro monitors cloud service 24/7 and has a response team on call 24/7 to respond to security incidents. Our hosting provider, AWS, also provides 24/7 global monitoring and support for the multi-location data centers that are used for Deskpro Cloud.
Vulnerability scanning is undertaken across the network to identify any potentially vulnerable systems and allows the security team to quickly review any weak points.
Deskpro doesn’t store credit card data. We use external PCI compliant services (Spreedly and Stripe) to provide billing services. Your credit card data momentarily passes through our servers, and for this reason, we are verified as Payment Card Industry Data Security Standard (PCI DSS) compliant.
We have a dedicated Quality Assurance (QA) department that tests, reviews and triages our code base. For every update or release to the software, testing is performed by development, support and QA teams with a multi-level approach.
There are separate environments for both staging and testing. These environments are separated both logically and physically from the live-production environment. No customer data is used in testing or development.
Deskpro is tested with unit testing, human auditing, application penetration testing, static analysis and functional tests. Third party penetration testing is also completed on an annual basis.
Deskpro has been built to mitigate common attack vectors; such as SQL injection attacks and cross-site scripting attacks (XSS). Deskpro Cloud also takes advantage of CloudFlare's enterprise-grade Web Application Firewall (WAF) to automatically block or challenge suspicious requests.
All customer data stored encrypted on AWS servers (with the AES-256 encryption algorithm).
Any data that is transmitted into and from the Deskpro platform is encrypted over the wire in line with industry best practices. Web traffic over HTTP is secured by CloudFlare with TLS 1.2 or 1.3 using proven-secure cipher suites. More information about SSL/TLS at CloudFlare.
Admins can configure multiple options for SSO to the Deskpro platform, including OneLogin, Okta, Azure, SAML, and JWT authentication. There are different configuration options available for SSO enabling you to customize how it interacts with agents/customers.
Deskpro enables 2FA through your SSO provider for admins, agents, and customers.
The Deskpro API is a REST-based API that runs securely over HTTPS. API requests can only be made by verified customers. API Authentication can be done through OAuth, API keys, or using short-lived API tokens.
Customizable Password Policies can be enabled for both agents and customers. This includes the ability to set minimum password length, forbidding password reuse, a mixture of numbers and characters, and forcing customers to change their password after a certain amount of time.
Comprehensive audit logs are kept for changes made by administrators. They provide records including type, action, performer and timestamp that it was executed. Activity logs for agents can also be viewed by admins, showing activity such as ticket replies or online time.
Deskpro maintains a high level of availability on the cloud platform, averaging over 99.9%. There is a publically available status page, where you can check the status of the cloud software and its components.
We use AWS with redundancy over at least two availability zones, with database backups offering 35-days worth of point-in-time recovery if needed. Additional encrypted off-site backups are updated daily.
We have established procedures and policies with regards to responding and communicating about security incidents from our Security Team.
The level of the security incident will dictate how we communicate and respond to our customers. If a security incident does occur, you will be kept updated via our Customer Success team. They will be on hand to help and support you through the incident regarding updates.
All of our procedures and policies regarding responding to security incidents are evaluated and updated on at least an annual basis.
In the case of an emergency or critical incident at any Deskpro premises, a business continuity plan has been put in place.
This was created so that we can continue to function as a business for our customers, no matter the scenario. The business continuity plan is tested and checked on an annual basis for applicability and any additional improvements that could be made.
Should you no longer wish to use Deskpro, we maintain backups of your accounts for 60 days - after which your data is completely deleted from all our systems.
Primary backups offer point-in-time recovery for 35 days. Encrypted offsite backups are updated daily.
Your data is securely deleted immediately from our primary data stores upon request. Encrypted offsite backups of your data get purged through regular backup rotation every 60 days.
Any hardware no longer in use is fully wiped and disposed of using regulated disposal service in accordance with ISO27001 compliance.
Before anyone joins Deskpro as an employee, their workstation is set-up and configured to comply with all of our security policies. These policies require that all workstations are configured to a high level and comply with security certification standards such as ISO27001 & Cyber Essentials Plus.
Each workstation has data encrypted at rest, strong passwords (managed by a secure password management vault), location tracking enabled and screens automatically turning off when idle.
SA central management system is used to monitor, track and report on malware, unauthorized software and removable storage devices. This is to ensure that all workstations are up to date with patches and security. We also have a strict non-removable storage device policy.
Any mobile devices (phones or tablets) used for work purposes are part of a mobile device management system for location tracking, secure passwords and SSO.
All new hires are screened during the hiring process. On commencement of employment at Deskpro, employees, contractors and cleaning crews are required to sign a Non-Disclosure and Confidentiality agreement. This is also an up-held post-employment contract.
Only certain people within the organization are given access to sensitive information. It is on a need-to-know basis with role-based permissions, to enable employees to perform their job to the best of their ability.
Our access control policy is implemented internally and within Deskpro we have multiple levels of security clearance. Some access, such as extended support or screen-sharing scenarios is performed on a client-agreement basis.
To increase the security even further, Deskpro uses Two Factor Authentication (2FA) for systems that contain sensitive or personal data.
The use of Single Sign On (SSO) for employee’s enables management to disable or change access to all applications instantly. This is used when an employee leaves Deskpro or their access needs to be removed.
As part of our internal password policy, Deskpro requires all employees to use an approved password manager. This is to ensure passwords are strong, kept in a secure location, regularly changed and not re-used. Where necessary, the password manager alerts users to any potential password risks to maintain high-level security at all levels.
In order for Deskpro to run efficiently, we rely on sub-service organizations to help us deliver our service.
When selecting a suitable vendor for a required service, we take the appropriate steps to ensure that the security and integrity of our platform are maintained. Every sub-service organization is heavily scrutinized, tested and security checked prior to being implemented into Deskpro.
Deskpro monitors the effectiveness of these vendors and they are reviewed annually to confirm their continued security and safeguards are being upheld. View a list of our current sub-service organizations.
In any situation where the use of one of these sub-service organizations could potentially impact the security of Deskpro, we take appropriate steps to mitigate the risk. This includes establishing agreements and ensuring that they are compliant with relevant certifications or regulations, such as GDPR.
Deskpro is always actively searching, monitoring and improving our security set-up. This is through regular checks and assessments from both our internal security team and 3rd party assessors.
All results are shared with the management team and discussed in-depth at security management reviews. Recent security audits and certifications include ISO27001, PCI, Cyber Essentials Plus, CSA Star, G-Cloud 12 & GDPR Readiness. You can view our list of certificates at the bottom of this page.
Our access control policy is implemented internally and within Deskpro we have multiple levels of security clearance. Some access, such as extended support or screen-sharing scenarios is performed on a client-agreement basis.
Independent penetration testing by a certified CREST CHECK 3rd party is carried out on at least an annual basis. The penetration tests performed are focused on security, infrastructure and product. Results of these tests are shared and acted upon by both the Security and Higher Management teams.
Our annual testing also includes both external and internal network vulnerability scans, with certification for Cyber Essentials Plus. All 3rd party penetration tests are carried out by consultants certified to CREST standards.
We appreciate that in certain circumstances, an organization may require further audits or penetration testing to be conducted, before the purchase of Deskpro can be made. We welcome customers to perform their own penetration testing on a Deskpro environment. If you wish to arrange one, please contact support for scheduling this, and for further pricing.
If you are a security expert or researcher, and you believe that you have discovered a security-related issue with Deskpro’s online systems, we appreciate your help in disclosing the issue to us responsibly. We have a Responsible Disclosure program. We ask the security research community to give us an opportunity to correct a vulnerability before publicly disclosing it.